| Roding, Germany
High-Secure Document Life Cycle
Identification documents are not just a piece of plastic, but high-secure auxiliaries for every citizen of age to actively participate both in an analogue and a digitalized world. The proper identification of citizens is a vital component of a well-functioning society – no matter if it is about political, social, cultural and economic participation or international travel. However, this delicate balance can be disarranged by criminals and fraudsters who spare no effort to steal and fake identities. Thereby, they do not only harm the individual as such, but also the whole of society. That is why slashing ID fraud and identity theft, improving document security and creating an infrastructure of trust are high on the agenda of governments and authorities around the world.
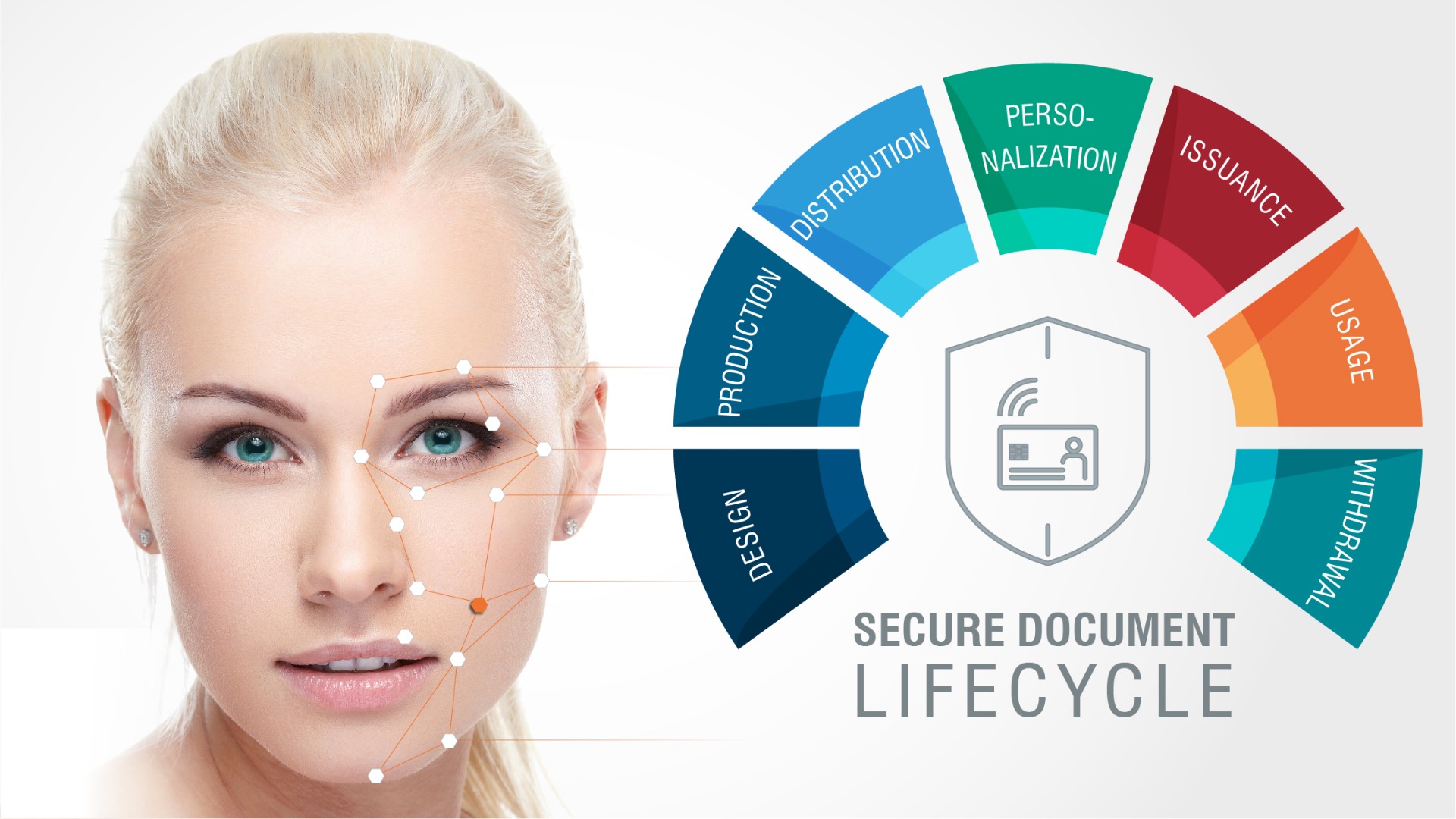
But how can ID documents be designed, produced, distributed, personalized, issued, used – and possibly withdrawn – in the most secure and reliable way?
The DESIGN of a secure identity document is science and art in union. The process does not only require skilled and well-experienced designers, graphic artists and security experts, but also a clear vision and understanding of the identity document’s intended purpose: Shall it be a national or an international ID document? Which security features shall be included in the document? We can resort to a variety of security features, most of which are endowed with microscopic printing figures or specific color-shifting characteristics which would make any attempts by forgers to tamper with the document immediately visible. To provide even more reliable protection against copying, the document design may include holograms or security inks which reveal their unique effects in specific angles or when illuminated with infrared or ultra-violet light.
Another vital part of ID document life cycle management, the PRODUCTION process, takes place in a high-security production facility. Regarding the security of the production site, international standards, e.g. the IT security guideline ISO 27001, define common security guidelines for the IT systems used. Furthermore, a company’s certification as Security Printer (according to ISO 14298) and as Security Supplier (according to CWA 15374) guarantees total compliance with all required security standards.
To provide reliable information about the life cycle of every single secure document, tracking and documenting the material usage of raw materials, intermediate materials and the final products is crucial. This requires track and trace of every single action of operators, service engineers and all software programs and tools involved in the production process.
A safe storage of blank documents is essential, especially during the DISTRUBUTION process. To avoid security gaps in the document life cycle, it is recommended to store the ready-for-delivery blank documents in a vault, securely transport them in dedicated transportation vehicles and, once they have reached their destination, store them in a secure and manipulation-save warehouse. To make this process even more secure, one can resort to a technique which combines production and personalization in one process step: Every single document is already pre-personalized with dedicated personal information (e.g. the color facial image or textual elements). Therefore, there are no more blank documents in circulation which could potentially be used by fraudsters. The ID document production of the Republic of Bosnia and Herzegovina serves as a vivid example in this case.
During the PERSONALIZATION process, the citizen’s personal data are applied to the blank document. But first of all, the personal data have to be acquired in a secure and reliable way – another possibly weak point in document life cycle management: During the document application process, the applying citizen’s identity must reliably be determined, usually by presenting a valid birth certificate. However, in this case, the document authentication might pose a challenge, as the birth certificate may either be very old, from a foreign issuer or printed on plain paper.
This process can be simplified and streamlined by means of self-service kiosks which limit the effort of additional operators. Kiosks automatically capture face images, fingerprints and signature, as well as read already existing ID documents. The verified data is then stored in a civil register and may be enriched with further data (e.g. updated pictures or addresses) over time.
Furthermore, another important link in the chain, the civil register, must be protected and securely connected to the personalization management system. By means of the user management, to which all systems are connected, the life cycle of the secure ID document can seamlessly be documented. The personalization management may be connected to further external system to provide data preparation or cryptographic functions. In its Doc. 9303, ICAO, an organization of the United Nations, defines valid data preparation guidelines for electronic Machine Readable Travel Documents (eMRTD), including name truncation, splitting or chip data generation. These guidelines guarantee international interoperability and document acceptance and thus ensure document security.
During the ISSUANCE process, the secure ID document is handed over to the corresponding document holder. Before the ID document is officially issued, a verification needs to be conducted to prevent the high-secure document from being delivered to the wrong applicant: For this very purpose, the biometric verification of fingerprints or face can be employed. To assure a seamless life cycle documentation of the ID document, operator and document tracking is mandatory.
The ID document’s actual USAGE takes the longest period of its life cycle. On a daily basis, it is used for the proof of identity, e.g. during elections, in casinos or shops, or when opening a bank account. However, the need for document security does not end here, as security also means permanent availability to users: The ID document’s lifetime is usually ten years. To ensure this high durability, the mechanical and electric parameters are important features which can already be influenced during the document’s design and production.
The WITHDRAWAL ofan ID document finally marks the end of its life cycle. The process usually combines the document’s physical destruction and logical revocation. Reasons for withdrawing a document can be manifold: For example, the document might have expired or have got lost so it is revoked with no physical access. Therefore, revocation lists have to regularly be updated to be able to promptly inform authorities not to accept the document if it is presented during a verification process. In addition, a compromized certificate, used for chip personalization, may case an ID document’s withdrawal.
To summarize, to reliably avoid identity theft and document fraud, the life cycle management of every single ID document in circulation requires the highest security level possible. From the very first design drafts of a document up to the document’s final destruction – every process step has to be carefully planned, managed and put into practice. To avoid friction and glitches between different stakeholders and create a document infrastructure of trust and security, one-stop shop providers can be entrusted high-secure national ID projects: Offering comprehensive government solutions from one single source, they implement individualized ID projects in a holistic and integral manner.
Press Contact:
Lara Schmaus
Phone: +49 9461 952 – 1579
Email: Lara.Schmaus@muehlbauer.de
